Introduction
Networking is where cyber defense meets reality. Every packet that enters or leaves your environment is a decision point: allow, deny, inspect, shape, or log. If you understand how networks actually work, you can shut down entire classes of attacks with a few well‑placed controls. Cybersecurity networking is one of the key requirements in ethical hacking.
This guide walks you from beginner concepts to advanced strategies—what to use, why it matters, and when each control is the right tool, backed by real‑world examples for Cybersecurity networking.

Fundamentals that matter to defenders
TCP/IP, ports, and protocols
- What it is: IP addresses for location, TCP/UDP for transport, and ports to identify applications (e.g., 443 for HTTPS).
- Why it’s used: ACLs, firewalls, and IDS/IPS match on IPs, protocols, and ports; fluency lets you write precise rules and triage alerts.
- When to use it: Always—in detection, response, and architecture reviews.
Real‑world example: A SOC analyst spots bursts of outbound connections to TCP 4444 from one workstation. Recognizing it as a common reverse shell port, they isolate the host and prevent exfiltration.
The OSI model as a map
- What it is: Seven layers from physical (cables) to application (HTTP, DNS).
- Why it’s used: Controls map to layers—802.1X (L2), IPsec (L3), TLS (L6/7), WAFs (L7).
- When to use it: During incident response to choose the right control point.
Real‑world example: An ICMP flood (Layer 3) is mitigated by upstream rate‑limits and edge filtering—no changes to web servers required.
Critical infrastructure pieces
- Endpoints and servers: Primary targets for compromise, must be monitored and patched.
- Switches and routers: Traffic directors; enforce policies between networks.
- DNS and DHCP: Identity hints for who is who, often abused by attackers.
- Firewalls: Policy gates; locate at egress, data center, and between sensitive zones.
Real‑world example: DNS response policy zones (RPZ) block newly registered malicious domains used in phishing, stopping callbacks automatically.
Core network controls
Protocol security
- Use secure admin protocols: SSH over Telnet, HTTPS over HTTP, SNMPv3 over v1/v2c.
- Disable legacy exposures: LLMNR/NetBIOS and TLS 1.0/1.1; prefer modern cipher suites.
- Email authenticity: SPF, DKIM, DMARC to curb spoofing.
Real‑world example: A switch exposes SNMP v2c “public.” Migrating to SNMPv3 with per‑role accounts ends the leak of device inventories and interface stats. This are vital in Cybersecurity networking.
- Defend against Layer‑2 tricks:
- ARP spoofing: Enable Dynamic ARP Inspection (DAI) and IP Source Guard.
- Rogue DHCP: Apply DHCP snooping on access switches.
- DNS poisoning: Use DNSSEC and DoH/DoT, plus RPZ to block known bads.
Wireless security – Cybersecurity Networking
- Enterprise auth: WPA3‑Enterprise with 802.1X and EAP‑TLS certificates.
- Management frame protection: Stop evil twin and deauth attacks with MFP/WIPS.
- Segmentation by SSID: Separate corp, guest, IoT onto distinct VLANs and policies.
Real‑world example: Conference “evil twin” SSIDs fail when clients require cert‑pinned EAP‑TLS and controllers enforce management frame protection.
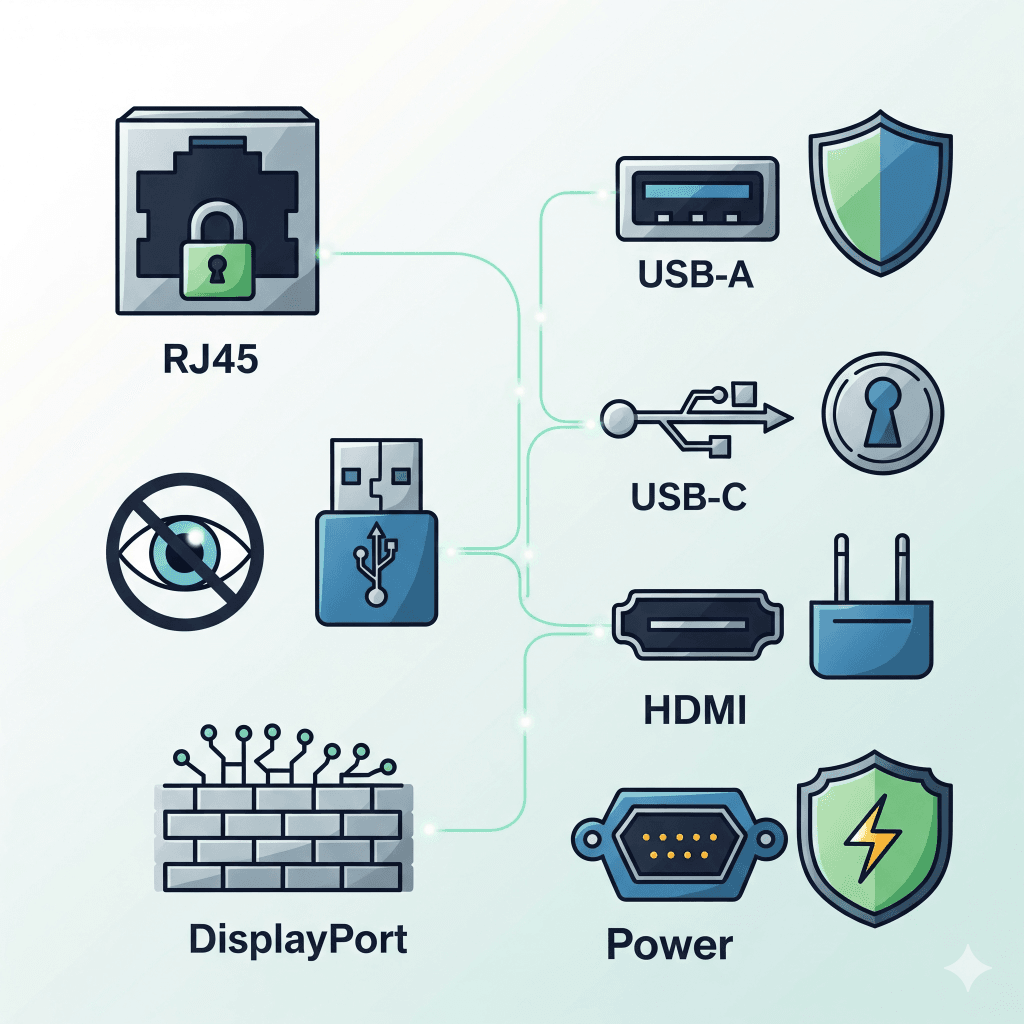
Device hardening and secure management IN
- Reduce attack surface: Disable unused services and ports, shut down unused switch interfaces.
- Strong admin access: AAA via RADIUS/TACACS+, per‑user accounts, MFA, role‑based authorization.
- Protect the management plane: Use a separate management VLAN or out‑of‑band network; restrict source IPs.
- Patch and config hygiene: Track advisories, version‑control configs, monitor drift, and encrypt backups.
Real‑world example in Cybersecurity Networking: A shared “admin/admin” device account enables rapid lateral admin compromise. Moving to AAA + MFA and per‑user roles blocks privilege escalation.
Segmentation and micro‑segmentation -Cybersecurity Networking
- Macro‑segmentation: Place high‑value assets in dedicated VLANs, gate inter‑VLAN traffic with firewalls, and adopt default‑deny.
- Micro‑segmentation: Enforce workload‑level policies (app tiers, identities), and block east‑west by default.
- Egress control: Define what each segment can reach on the internet; block unknown TLDs and uncategorized destinations.
Real‑world example in Cybersecurity Networking: Research labs are placed in private VLANs with narrow egress; when a lab device is compromised via phishing, it cannot pivot into finance or exfiltrate to random cloud storage.
Access and identity
VPN
- Types: Remote access (users to apps) and site‑to‑site (branch to HQ/cloud).
- Tunneling choices: IPsec for network‑layer, TLS‑based for app‑layer—use perfect forward secrecy.
- Split vs full tunnel: Balance performance with inspection and control.
Real‑world example in Cybersecurity Networking: Full‑tunnel with device posture checks blocks an unpatched laptop from reaching sensitive apps until compliant.
Zero Trust Network Access
- Principle: Grant app‑level access based on identity, device health, and context.
- Why: Reduce lateral movement; shrink exposure; better user experience than broad network access.
- When: Hybrid/multi‑cloud, contractors, and BYOD.
Real‑world example: Contractors get access to only three internal web apps with per‑request MFA—they never touch the internal network layer, eliminating pivot paths.
Network Access Control
- What it does: Validates device identity and posture before granting access (802.1X).
- Why it matters: Keeps unmanaged or non‑compliant devices off sensitive networks.
- How to use: Quarantine VLANs, guest flows, and dynamic VLAN assignment post‑auth.
Real‑world example: Devices without current endpoint protection are automatically placed in a remediation VLAN with patch services but no production access.
Perimeter and application defenses
- Layered firewalls: Edge, data center, and micro‑perimeter around high‑value apps; adopt default‑deny with documented justifications and review dates.
- IDS/IPS: Start with IDS to tune, then enable IPS for critical paths; pair with TLS decryption where appropriate or encrypted traffic analytics where not.
- WAF and API security: Enforce OWASP Top 10 protections, schema validation, rate limits, and bot defenses at API gateways.
- Egress policies: Allow‑list business destinations, restrict risky categories, and monitor rare ASN and new domain patterns.
Real‑world example: Finance VLAN can only reach the SaaS ERP over HTTPS and a vendor SFTP IP—shadow IT sync tools are silently blocked at egress.
Monitoring and incident response
Telemetry and analytics
- Collect the right signals: NetFlow/IPFIX, DNS/DHCP, proxy, firewall, VPN, and auth logs; add packet capture for deep forensics.
- Correlate with context: Tie flows to users, devices, and segments; align detections to MITRE ATT&CK.
- Automate safely: Use SOAR for containment actions like blocking domains, isolating hosts, and opening tickets with approvals.
Real‑world example: Outbound flows to rare ASNs paired with newly registered domains trigger an automated block and a case in the SOC queue with attached PCAP.
Network‑centric incident response
- Contain quickly: Shut switch ports, move to quarantine VLANs, update firewall/IDS policies, and blackhole or rate‑limit noisy traffic.
- Preserve evidence: Time‑sync devices (NTP), capture PCAPs, and preserve logs with integrity.
- Verify recovery: Patch, rotate credentials, then validate with targeted scans and watch for canary beacons.
Real‑world example: Ransomware spread via SMB is stopped by denying SMB between user VLANs and forcing access through a monitored, MFA‑protected file gateway.

Cloud, SD‑WAN, and SASE
- Cloud fundamentals: Use VPC/VNet segmentation, security groups/NACLs, private endpoints, bastion hosts, and service meshes for east‑west.
- Identity is the perimeter: Strict IAM, least privilege, just‑in‑time admin, and per‑app egress in cloud.
- SD‑WAN: App‑aware routing, branch segmentation, and resilient connectivity.
- SASE: Converge SWG, CASB, ZTNA, and FWaaS near users for consistent policy everywhere.
Real‑world example: A lift‑and‑shift app exposed admin ports to the internet; moving to private subnets, ZTNA for admin, and just‑in‑time access closes exposure without hurting developer velocity.
Specialized domains
OT and ICS in cybersecurity networking
- Constraints: Legacy protocols, safety‑critical uptime, and fragile devices.
- Controls that fit: Strict zoning and conduits, unidirectional gateways, and passive monitoring (no active scans in control networks).
- IR nuance: Coordinate with operations; change windows are limited.
Real‑world example: A water utility uses one‑way data diodes to move telemetry to IT while keeping control systems isolated—even if IT is phished, plant processes stay safe.
IPv6 security
- Dual‑stack blind spots: IPv6 may be on by default; attackers can exploit it while defenders watch IPv4.
- Threats: Rogue router advertisements, ND spoofing, and extension header abuse.
- Controls: RA Guard, DHCPv6 Guard, IPv6 ACLs, and disabling unused IPv6 where appropriate.
Real‑world example: A rogue RA makes an attacker the default gateway. Enabling RA Guard on access switches ends the interception instantly.
Validation and governance
- Continuous testing: Asset discovery, authenticated vulnerability scans, and pentests that include Wi‑Fi, VPN, and remote admin portals.
- Purple teaming: Emulate ATT&CK techniques; verify that detections fire and responses execute.
- Zero Trust as a program: Verify explicitly, least privilege, assume breach—identity‑first, network as policy fabric, telemetry as trust signal.
- Policy and change management: Peer‑review firewall and router changes, track rule owners and expiry, and map data flows for sensitive systems.
Real‑world example: A quarterly firewall review removes 120 stale rules; troubleshooting speeds up and the blast radius shrinks dramatically.
Case studies and implementation roadmap in cybersecurity networking
Case studies
- Ransomware contained by design:
- Context: Flat network; weak SMB controls.
- Actions: VLAN segmentation, SMB signing, NDR + SOAR isolation.
- Outcome: 12 endpoints encrypted; ERP and backups safe; recovery in hours.
- Data exfiltration stopped at egress:
- Context: Odd outbound flows after hours.
- Actions: NetFlow + DNS correlation, egress allow‑lists, PCAP confirmation.
- Outcome: Host isolated; creds rotated; no data lost.
- Remote healthcare secured:
- Context: Rapid telehealth rollout.
- Actions: ZTNA for EMR with posture checks, WPA3‑Enterprise, NAC for medical devices.
- Outcome: No regulatory findings; phishing no longer grants broad access.
0–90 day roadmap
- Asset inventory: Discover networks, devices, apps; document ownership.
- Baseline hardening: SSH/HTTPS only, SNMPv3, AAA + MFA, disable legacy protocols.
- Quick segmentation: Separate guest, corp, IoT; default‑deny inter‑VLAN.
- Logging pipeline: Centralize DNS, DHCP, firewall, VPN, auth, and NetFlow.
- Egress policy: Allow‑list business destinations and safe TLDs; block risky categories.
90–180 day roadmap
- ZTNA pilot: App‑level access for contractors; retire broad VPN for them.
- Detections: Map to ATT&CK (C2, lateral movement, exfil); tune for low noise.
- Micro‑segment HVAs: Apply identity‑aware policies to top five crown‑jewel apps.
- Wi‑Fi uplift: WPA3‑Enterprise + 802.1X; enable WIPS where needed.
6–12 month roadmap
- SOAR automation: Standardize quarantine, blocks, and ticket flows with approvals.
- SASE/SD‑WAN: Roll out for branches to get consistent policy and performance.
- Purple teaming: Quarterly control validation; fix gaps fast.
- Cloud posture: Private subnets, service mesh, just‑in‑time admin, per‑app egress.
Read More:
FAQs
- What’s the difference between IDS and IPS?
IDS detects and alerts; IPS sits inline and blocks. Tune in IDS first, then enforce in IPS on critical paths. - Should I use full‑tunnel or split‑tunnel VPN?
Full‑tunnel offers stronger inspection and egress control; split‑tunnel can perform better. Use full‑tunnel for sensitive roles and unmanaged networks.
- How do I secure APIs exposed over the internet?
Authenticate and authorize every call, enforce rate limits, validate request/response schemas, require TLS 1.2+ with modern ciphers, and place a WAF/API gateway in front to filter injection, deserialization, and abuse. Monitor with per‑endpoint metrics and alert on spikes or unusual clients. - What’s the difference between a WAF and an API gateway?
WAFs protect primarily web applications (HTML/JSON) from OWASP Top 10 risks. API gateways add developer‑centric controls like token validation, scope/claim checks, schema enforcement, and per‑client throttling. Use both when APIs back web apps. - How aggressive should egress filtering be?
Start with default‑deny and allow only destinations and ports your business needs (e.g., specific SaaS, update services, and DNS). Maintain an exception process, monitor new domains and rare ASNs, and periodically prune exceptions. - Is IPv6 worth securing if we “don’t use it”?
Yes. Many OSes enable IPv6 by default. Attackers can abuse rogue router advertisements or ND spoofing even if you ignore IPv6. Apply RA Guard, DHCPv6 Guard, and IPv6 ACLs—or disable IPv6 where appropriate after impact analysis. - How long should I retain network logs?
Balance compliance and cost. Common baselines: NetFlow/DNS/auth for 90–180 days, firewall/VPN for 180–365 days, and longer for regulated data. Use tiered storage and summaries (e.g., hourly aggregates) for long‑term trend analysis. - How do I reduce SIEM noise from network detections?
Baseline normal traffic by time of day and segment, use allow‑lists for known services, apply rare‑event rules (e.g., new domains, rare ASNs), and correlate across signals (DNS + flow + auth) before alerting. Iterate with purple teaming. - What’s the quickest way to get value from micro‑segmentation?
Start with your top five high‑value applications. Map flows, enforce default‑deny east‑west, and create identity‑based allow rules for required service calls. Measure with before/after lateral path counts and failed connection logs. This is important in cybersecurity networking. - How do I secure remote admins and jump access?
Use bastion hosts behind ZTNA with per‑session recording, just‑in‑time access, MFA, and IP allow‑lists. Disable direct admin ports from the internet and branch sites. Rotate credentials and enforce strong SSH/TLS settings. - What are practical DDoS defenses for a small team?
Enable upstream scrubbing with your ISP or a cloud DDoS service, implement rate limits and connection tracking at the edge, and deploy a CDN/WAF for public apps. Pre‑stage blackhole/community routes and have a runbook with contacts. - How do I safely inspect encrypted traffic?
For corporate devices, use TLS decryption at secure gateways with strict privacy and exception policies. Where decryption isn’t possible, apply encrypted traffic analytics (SNI, JA3/JA4, flow features) and behavioral detections. - Do I still need VPN if I roll out ZTNA?
Often yes, but for fewer use cases. Keep VPN for legacy protocols, bulk administrative workflows, and site‑to‑site needs. Prefer ZTNA for routine user access to apps. - What’s the best way to learn this hands‑on?
Build a home lab (virtual switches, routers, a firewall VM), practice VLANs, ACLs, NAT, and VPN. Capture traffic with Wireshark, generate logs, and write SIEM detections for your own lab scenarios.
Conclusion
Networking is where threats move—and where defenders can stop them cold. Master the fundamentals, then layer in segmentation, identity‑centric access, and rigorous monitoring. Treat egress as a controlled boundary, validate with testing and purple teaming, and evolve toward Zero Trust. With these practices in place, you shrink the attack surface, limit blast radius, and turn your network into an adaptive defense system.


